Trezor Login: Secure Access to Your Crypto Wallet
A complete guide to logging in, verifying security, and managing your Trezor account
Why Trezor Login Security Matters
Accessing your cryptocurrency safely begins with logging in to your Trezor wallet. The Trezor login process is not just a simple sign-in—it ensures that your private keys remain protected, that your device is genuine, and that your crypto assets are safe from cyberattacks. With Trezor, every login involves multiple security layers, from PIN entry to optional passphrases, keeping your digital assets secure even if your computer is compromised.
Whether you are a first-time user or an advanced crypto investor, understanding the login process helps you prevent phishing attempts, protect recovery seeds, and make the most of your Trezor wallet.
Quick Pro Tip:
Always log in through the official Trezor interface or Trezor Suite. Never enter login details on third-party websites or links sent via email, as these may be phishing attempts designed to steal your crypto.
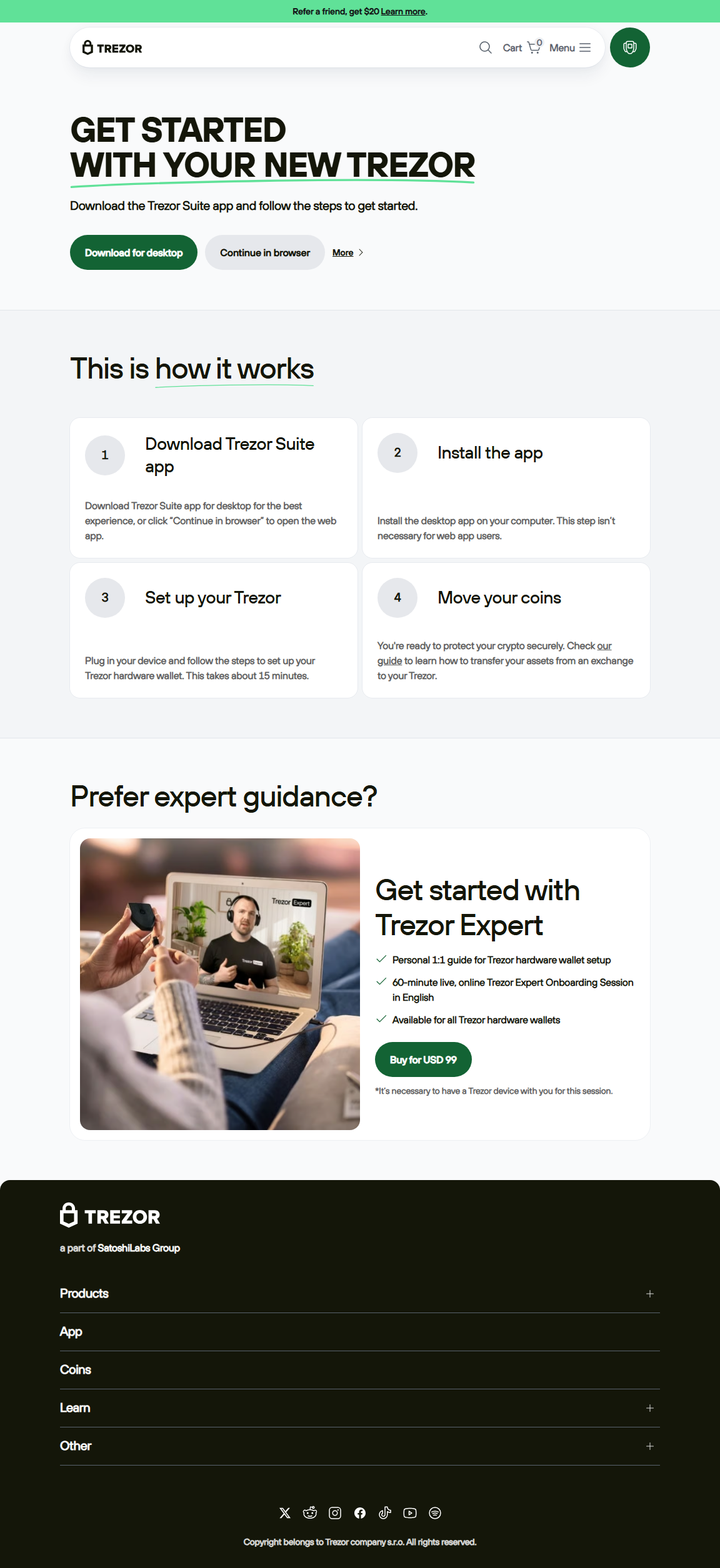
Step-by-Step Guide to Logging in to Trezor
Key Security Features During Login
Trezor login is built to protect your crypto from start to finish. Every login involves device authentication, PIN verification, and optional passphrase entry. Even if your computer is compromised, the device and recovery seed remain secure. The login process also ensures your firmware is verified, preventing malicious software from intercepting your assets.
Pro Insight:
Use a separate hidden wallet for sensitive assets. Entering a unique passphrase creates a secondary wallet invisible without the correct passphrase. This adds a crucial layer of privacy and security.
Common Issues with Trezor Login
- Incorrect PIN: Entering the wrong PIN too many times temporarily locks the device. Take care to enter it accurately.
- Firmware Outdated: Trezor Suite will prevent login until the device firmware is updated.
- Passphrase Forgotten: Lost passphrases for hidden wallets cannot be recovered. Keep them safe offline.
- Phishing Attacks: Only log in through official Suite or Trezor.io/start.
FAQs About Trezor Login
A: Yes. Trezor Suite supports mobile devices, but using a secure desktop is recommended for initial logins and firmware verification.
A: You can restore access using your 24-word recovery seed on a new Trezor device. Without the recovery seed, funds are irretrievable.
A: Each Trezor wallet can support multiple hidden wallets via different passphrases, but simultaneous logins are not supported.
A: Trezor Suite automatically verifies the device firmware and authenticity before allowing any login.
Comparison Table: Hardware vs Software Login
| Feature | Hardware Wallet Login | Software Wallet Login |
|---|---|---|
| Security | Offline device, PIN, passphrase, verified firmware | Online only, vulnerable to malware or phishing |
| Recovery | 24-word recovery seed | Dependent on account/password recovery |
| Ease of Use | Guided via Trezor Suite | Varies by app |
| Cost | $60–$200 | Mostly free |
Advanced Login Tips for Crypto Enthusiasts
- Multi-Wallet Management: Use passphrases to create hidden wallets for separating assets.
- Firmware Updates: Always verify device updates before login to prevent exploits.
- DeFi Access: Log in securely to interact with decentralized finance platforms without exposing private keys.
- PIN Complexity: Avoid simple PINs. Longer, randomized PINs prevent brute-force attacks.
Final Thoughts on Trezor Login
The Trezor login process is your first line of defense in securing your crypto assets. Using official access points, verifying firmware, and leveraging optional passphrases and hidden wallets ensures maximum protection. Whether you’re a beginner or experienced crypto user, following these steps protects your assets and gives peace of mind. Treat your recovery seed and passphrases with care, always confirm the device’s authenticity, and enjoy secure access to your cryptocurrency through Trezor.